There is an effort to implement Curve25519-based algorithms in WebCrypto: webcrypto-secure-curves/explainer.md at 0874265053dcace299f52c1c9e6b1f2e925e0aa2 · WICG/webcrypto-secure-curves · GitHub
There’s also a specification: Secure Curves in the Web Cryptography API
Lots of people at fission have been excited about this!
Try it out
According to this page you can try out Curve25519-based WebCrypto APIs in chrome/chromium today!
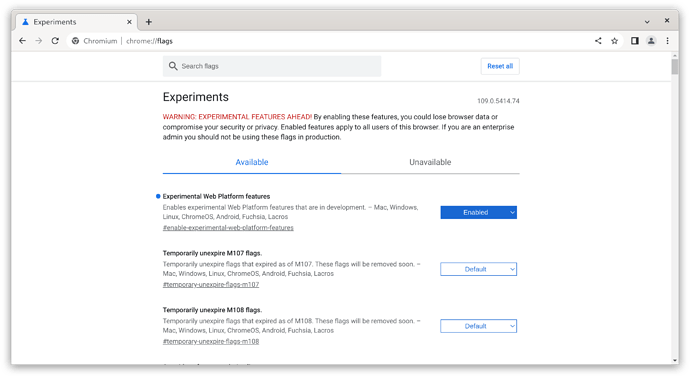
Let’s do this! First we need to navigate to about:flags:
Search for “Experimental Web Platform features” and change the dropdown on the right from “Default” to “Enabled”.
It’ll prompt to reload the window. After doing that and coming back to about:flags, it should look like in the screenshot.
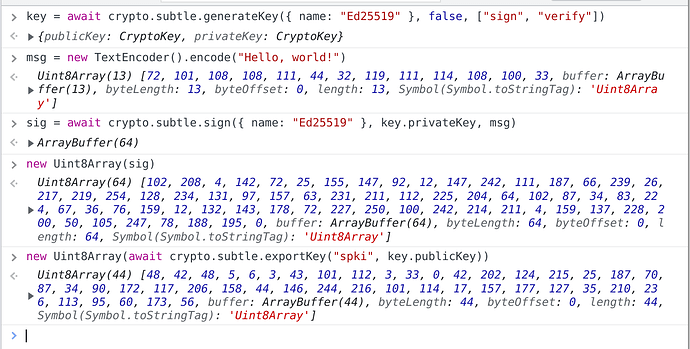
You can now open up the DevTools on any HTTPS-based website where WebCrypto is usually supported and play with Curve25519:
Interesting observations so far: I’m on version 109.0.5414.74 chromium, and it only supports exporting “spki”, but not “raw” or “jwk” formats that are in the specification linked above.
Other browsers
The “intent to prototype” was tracked here: https://groups.google.com/a/chromium.org/g/blink-dev/c/n0uKIqfypW0/m/xu5UBbaBAwAJ
Mostly it’s chrome and firefox teams that have so far committed to doing so.
We’re still waiting for more concrete answers from the Safari team: Curve25519 in WebCrypto · Issue #67 · WebKit/standards-positions · GitHub
Status
For Blink, the implementation is tracked here: 1370697 - chromium - An open-source project to help move the web forward. - Monorail
It seems to be stuck on some other work, specifically regarding rejecting small-order keys: X25519 in Web Cryptography · Issue #271 · mozilla/standards-positions · GitHub
Another issue being discussed is whether it’s worth changing the WebCrypto API so it’s not split into separate import/exportKey and operations functions, but instead doing these imports automatically in verify (IIUC): Error handling in key import of secure curves in Web Crypto · Issue #82 · WebKit/standards-positions · GitHub